Network Security Protocols to Avoid Hacking
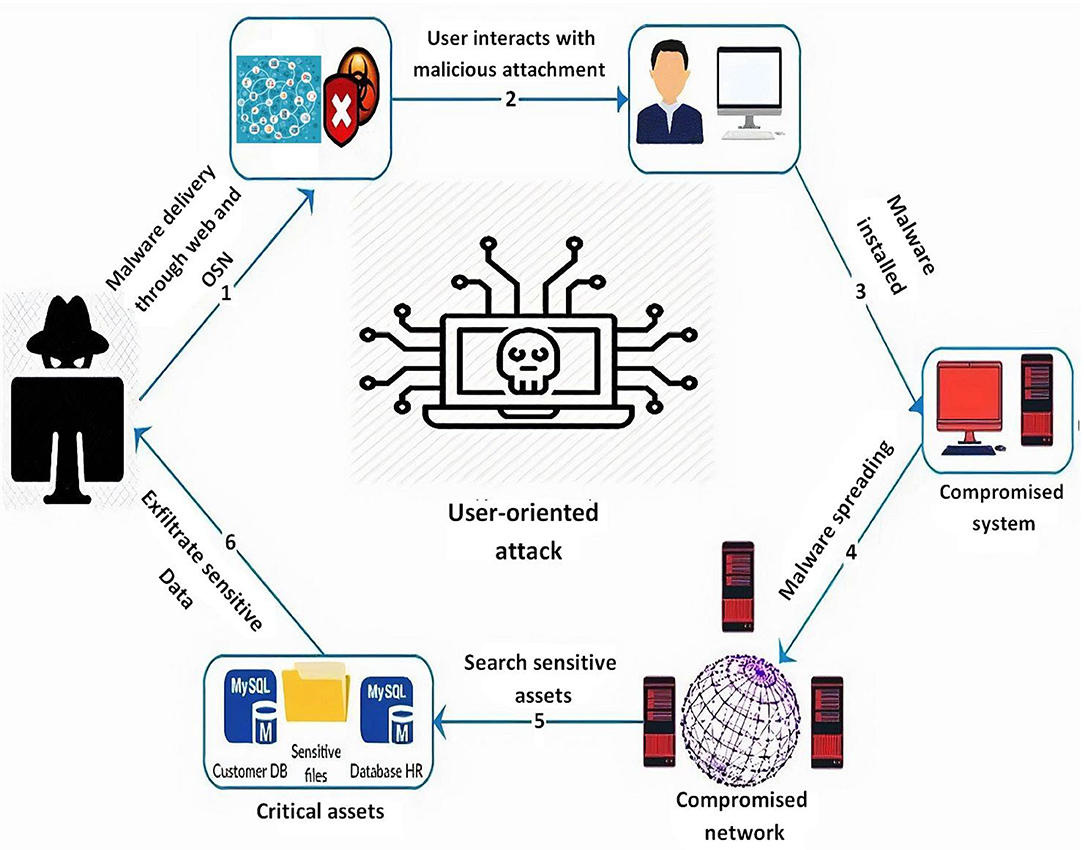
As technology advances, cybersecurity threats continue to evolve, and businesses of all sizes are susceptible to network security threats. In this article, we'll discuss the importance of implementing network security protocols to avoid hacking and explore five ways to prevent network security threats.
Understanding Network Security Protocols
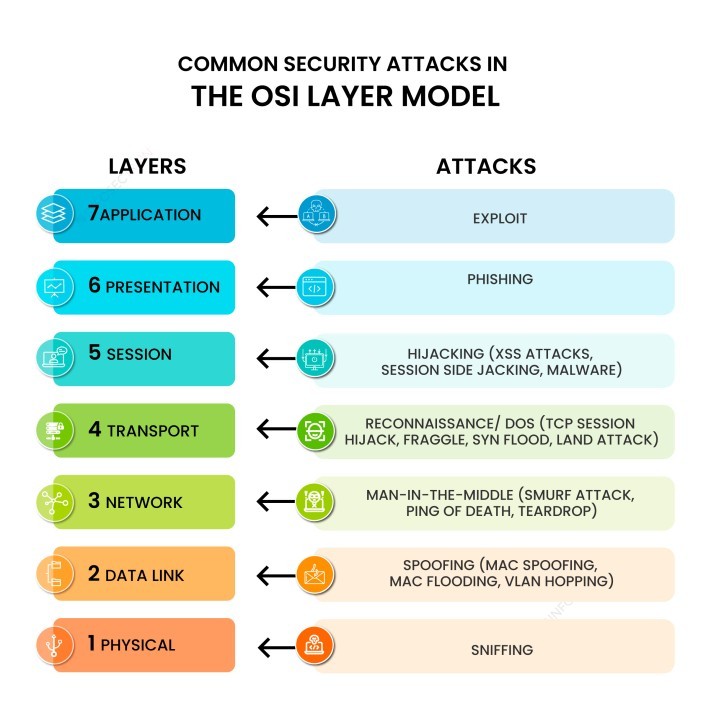
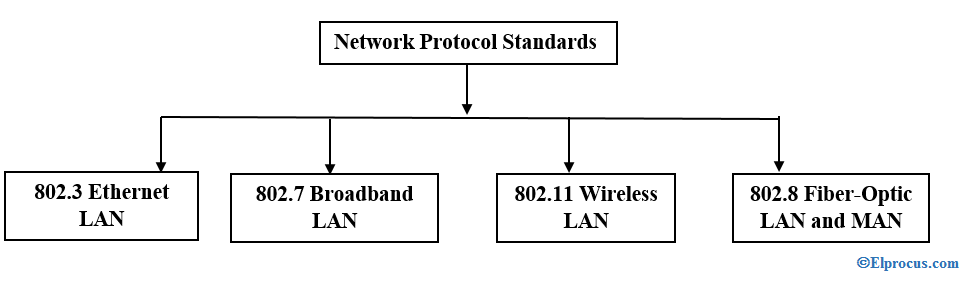
A network protocol is a pre-defined set of rules and processes that determine how data is transmitted between devices, such as end-user devices, networking devices, and servers. The fundamental purpose of network protocols is to ensure the integrity and security of data transmitted across network connections. Selecting an appropriate network protocol is crucial to prevent hacking threats.
Basic Network Security Protocols
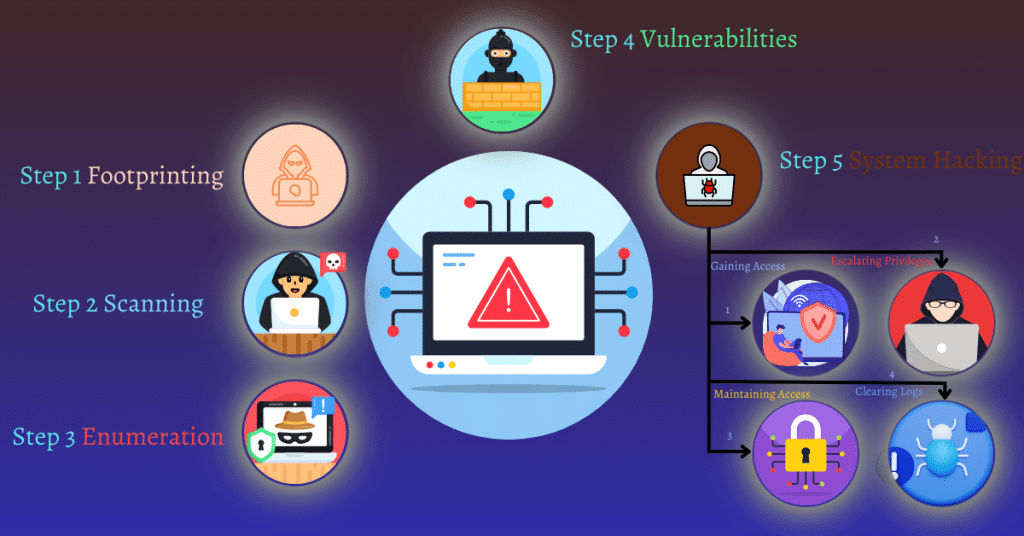
Early network security protocols were designed to prevent hackers from stealing or changing information to sabotage communications. However, as hacking techniques evolved, protocols had to change to keep pace. Some basic network security protocols include:
- TCP/IP: A suite of protocols that enables devices to communicate with each other over the internet.
- HTTP/HTTPS: A protocol used to transfer data between a browser and a web server, with HTTPS encrypting the communication.
- SSH: A protocol used for secure remote access to devices.
Advanced Network Security Protocols
To strengthen your organization's cybersecurity, explore various advanced network security protocols, such as:
- Kerberos: A protocol used for authentication and authorization.
- TACACS+: A protocol used for centralized authentication and authorization.
- Wireless Security Protocols: Such as WEP, WPA, and WPA2, used to secure wireless networks.

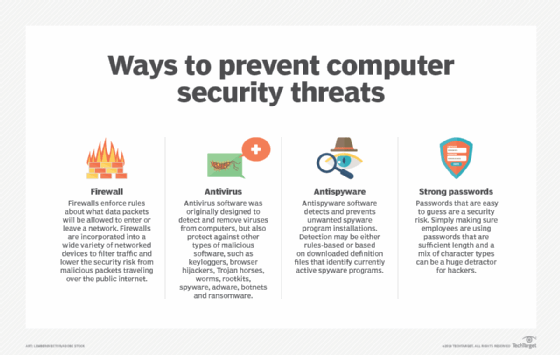
Network Security Best Practices
To prevent network security threats, businesses should implement the following best practices:
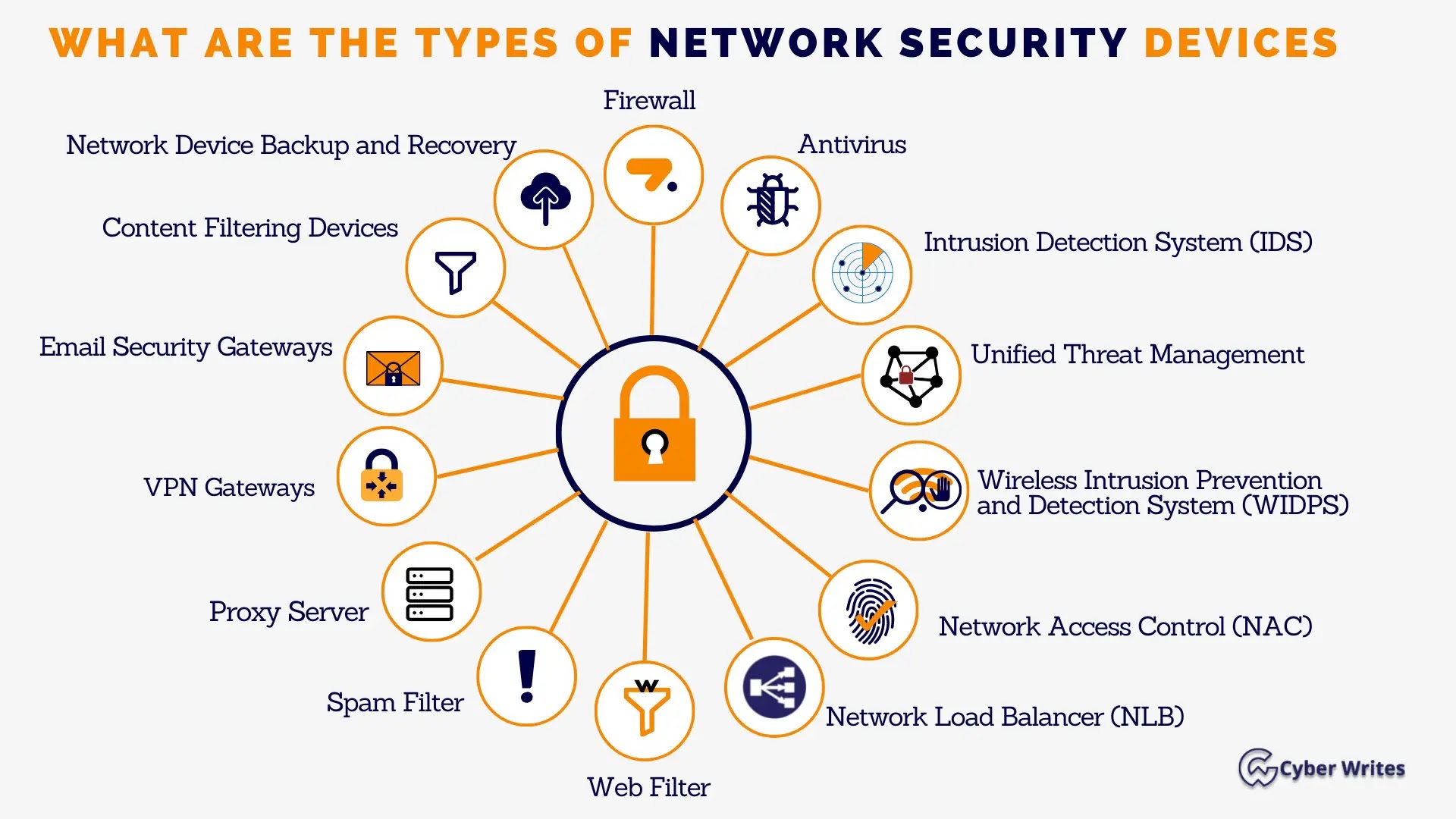
- Implement a firewall: A security system that monitors and controls incoming and outgoing network traffic.
- Use network segmentation: Divide the network into smaller segments to limit the spread of malware.
- Use data encryption: Encrypt sensitive data both in transit and at rest.
- Regularly update software and firmware: Keep devices and vulnerable system components up-to-date with the latest security patches.
- Use multi-factor authentication: Require users to provide multiple forms of verification to access devices and sensitive data.
Conclusion
Implementing network security protocols is crucial to prevent hacking threats. By understanding the importance of network protocols and implementing best practices, businesses can strengthen their cybersecurity and protect themselves from cyber threats.
Remember, cybersecurity is not a one-time task; it requires continuous effort and attention. Keep your devices and network security protocols up-to-date to prevent hacking and protect your business.
Additional Resources
- NIST Cybersecurity Resources: The National Institute of Standards and Technology (NIST) provides a wealth of cybersecurity resources, including guidelines, best practices, and standards.
- CISA Cybersecurity Best Practices: The Cybersecurity and Infrastructure Security Agency (CISA) provides information on cybersecurity best practices to help individuals and organizations implement preventative measures and manage cyber risks.
- CYBERSECURITY101: A learning platform that provides courses and resources to help individuals and organizations improve their cybersecurity skills.