Essential Guide to Internet Protocol Address Protection
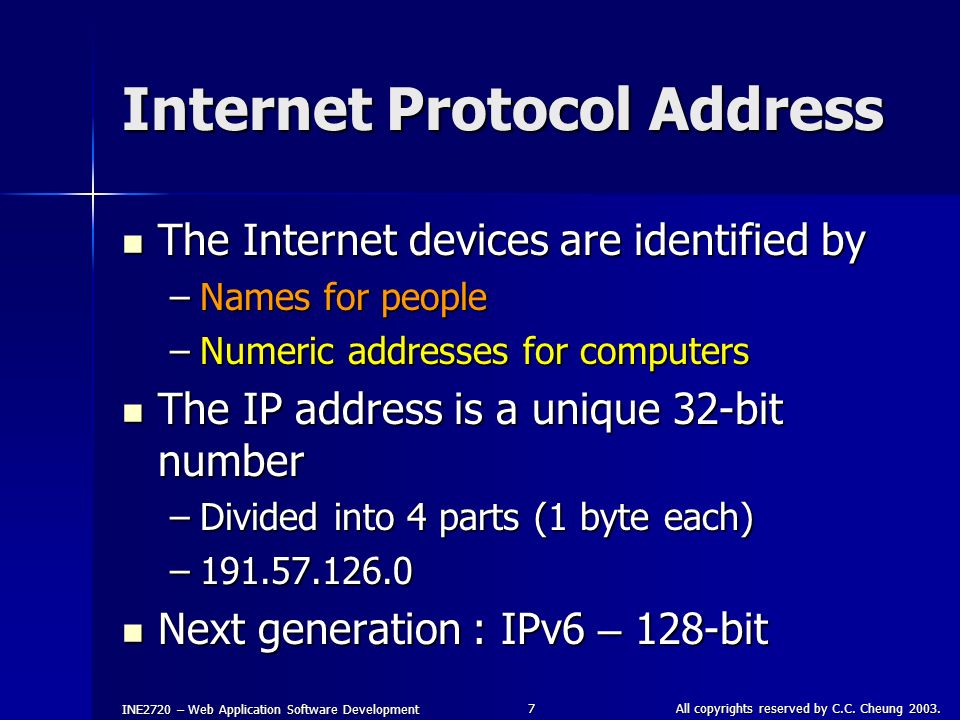
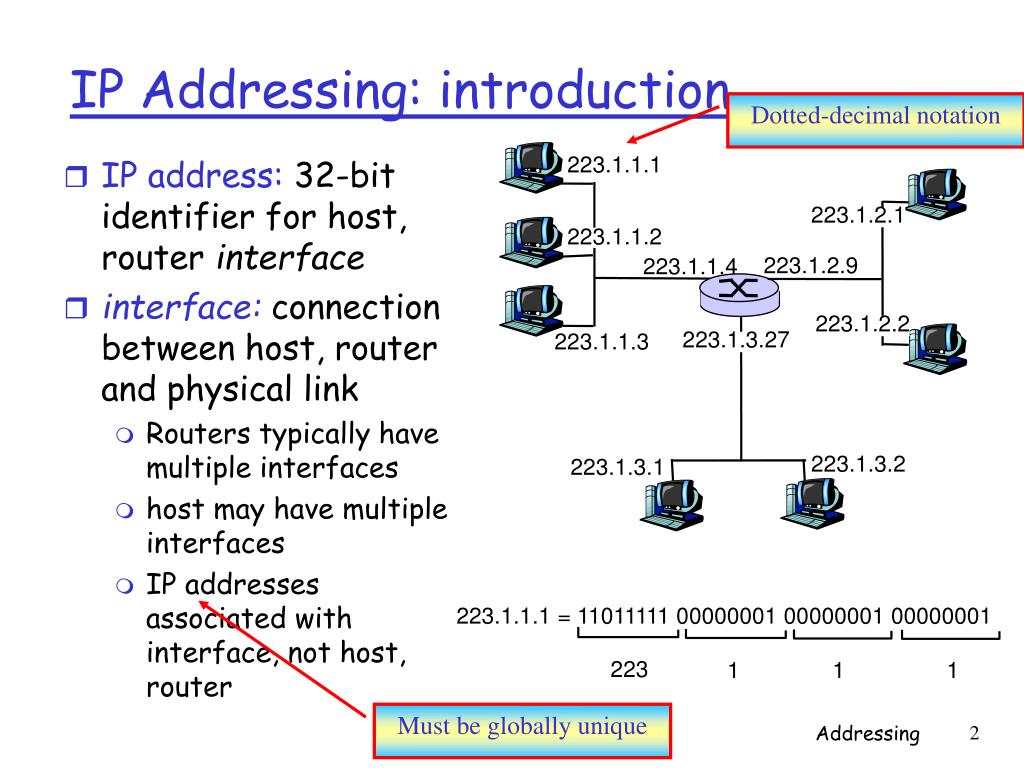
In the digital age, maintaining online security is crucial, and one crucial aspect of this is protecting your Internet Protocol (IP) address. An IP address is a unique number assigned to devices connected to a network, identifying them and enabling communication. However, this unique number can be used by malicious actors to access and exploit your device and personal data.What is an IP Address?
An Internet Protocol (IP) address is a unique number assigned to individual devices, like computers and mobile phones, connected to the internet or a network. It's a series of numbers separated by dots (e.g., 192.168.1.1), helping data packets to reach their intended destination. The Internet Protocol (IP) is the standard that enables data interchange between devices through a network.Why Do I Need IP Address Protection?
In the online landscape, exposing your IP address leaves your device vulnerable to various threats, including: * **IP Thefts**: Malicious actors can steal your IP address to impersonate you or track your activities. * **Unwanted Attention**: Your IP address can reveal your location and attract unwanted attention from marketing firms or hackers. * **Network Infections**: Unsecured IP addresses can lead to network infections that compromise all connected devices.Exploring Different Types of IP Security Protocols
To maintain online security, you need to familiarize yourself with various IP security protocols: * IPSec