Data Protection Techniques for Personal Use: A Comprehensive Guide
Data protection is a crucial aspect of safeguarding personal information in today's digital age. As technology advances, the risk of data breaches and identity theft also increases. In this article, we will discuss various data protection techniques for personal use, helping you to secure your sensitive information and maintain peace of mind online.
Why Data Protection Matters
With the proliferation of online services, social media, and personalized advertising, our personal data is being collected, stored, and shared more than ever before. This raises concerns about data protection and privacy. Failure to secure sensitive data can result in prosecution, severe fines, and damage to an individual's reputation.
Top Data Protection Techniques for Personal Use
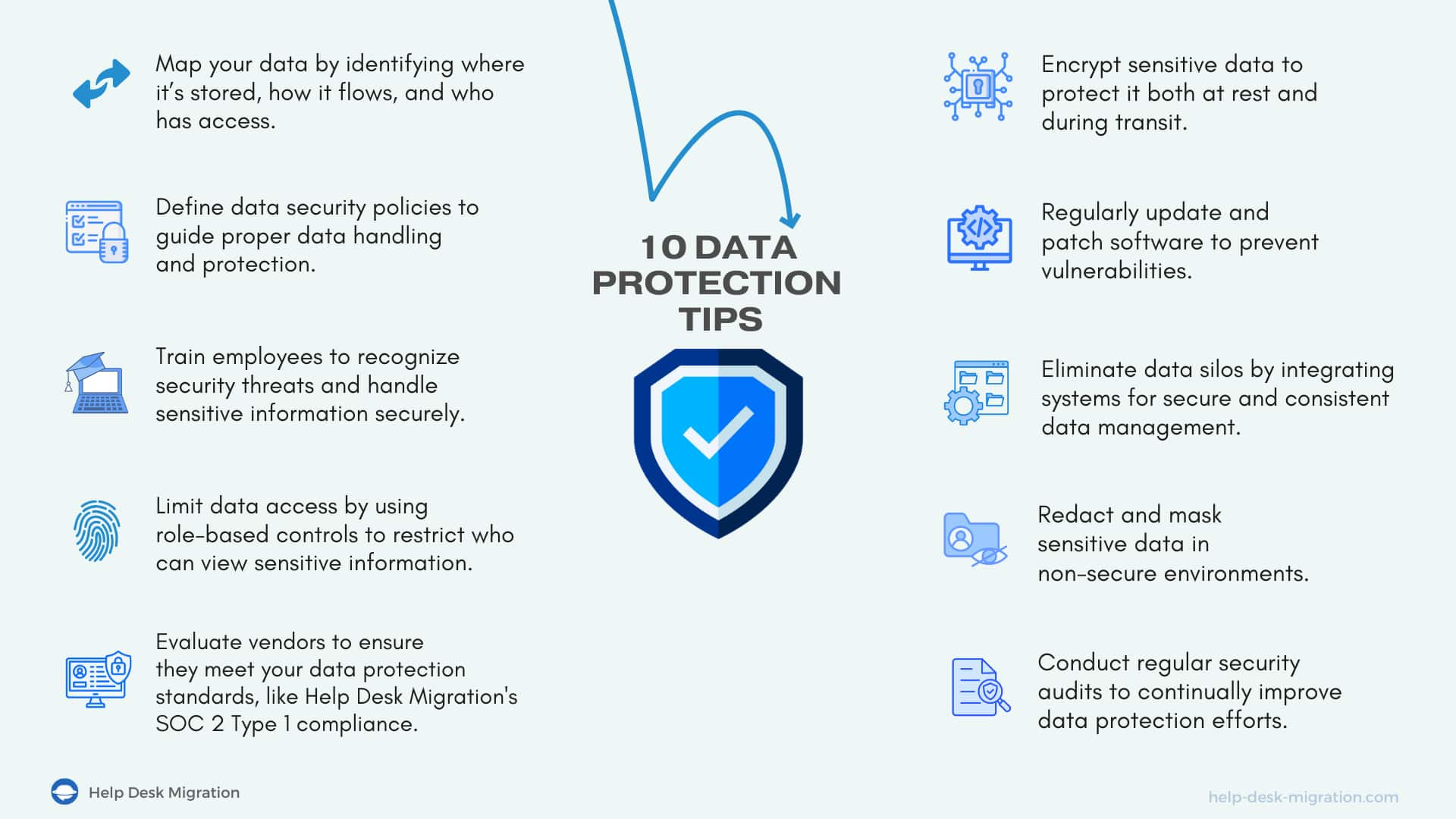
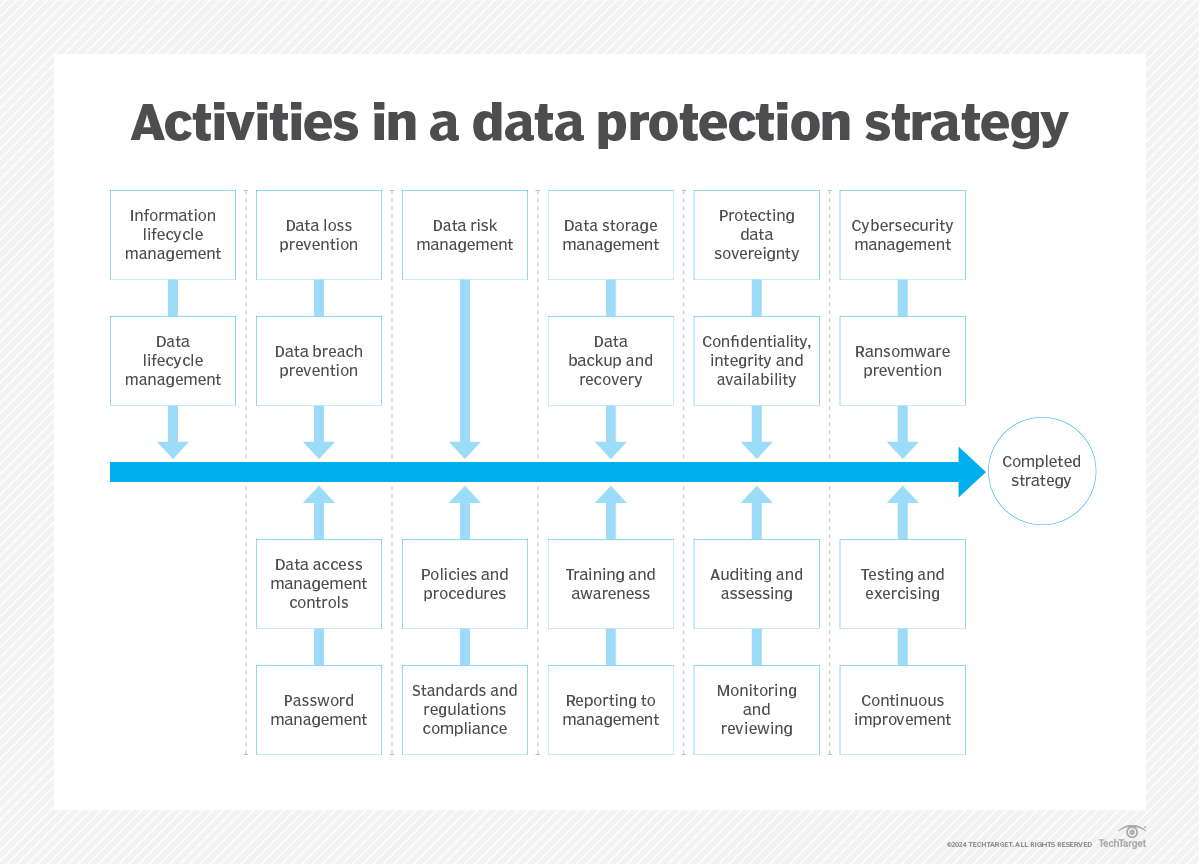
- 1. Encryption**: Encrypting your data is a powerful method to ensure it remains confidential and secure. Use a reputable encryption tool to protect your data both in transit and at rest.
- 2. Two-Factor Authentication**: Implement two-factor authentication (2FA) to provide an additional layer of security for your online accounts. This adds an extra step to the login process, making it more difficult for hackers to gain access.
- 3. Password Managers**: Utilize a password manager like NordPass to keep all your passwords, passkeys, credit card details, and other sensitive data safe and organized.
- 4. Data Anonymization**: De-identification techniques, such as data anonymization, can help mitigate privacy risks while maintaining the usefulness of data for analysis and research.
- 5. Secure Browsing**: Use a secure browser, such as Firefox or Tor, to protect your online activities from tracking and surveillance.
- 6. Regular Backups**: Regular backups of your data ensure that it is retained and handled in a suitable manner. Consider using cloud storage services like Google Drive or Dropbox for secure backups.
- 7. Internet Security Software**: Install reputable internet security software, such as antivirus programs or firewall software, to protect your device from malware and other online threats.
- 8. Data Inventory**: Conduct a data inventory to identify and classify sensitive data, ensuring that it is properly protected and handled throughout its lifecycle.
- 9. Data Storage Tiering**: Implement data storage tiering to prioritize the storage and protection of sensitive data, separating it from less critical information.
- 10. Regular Security Audits**: Perform regular security audits to identify vulnerabilities and implement necessary measures to address them.

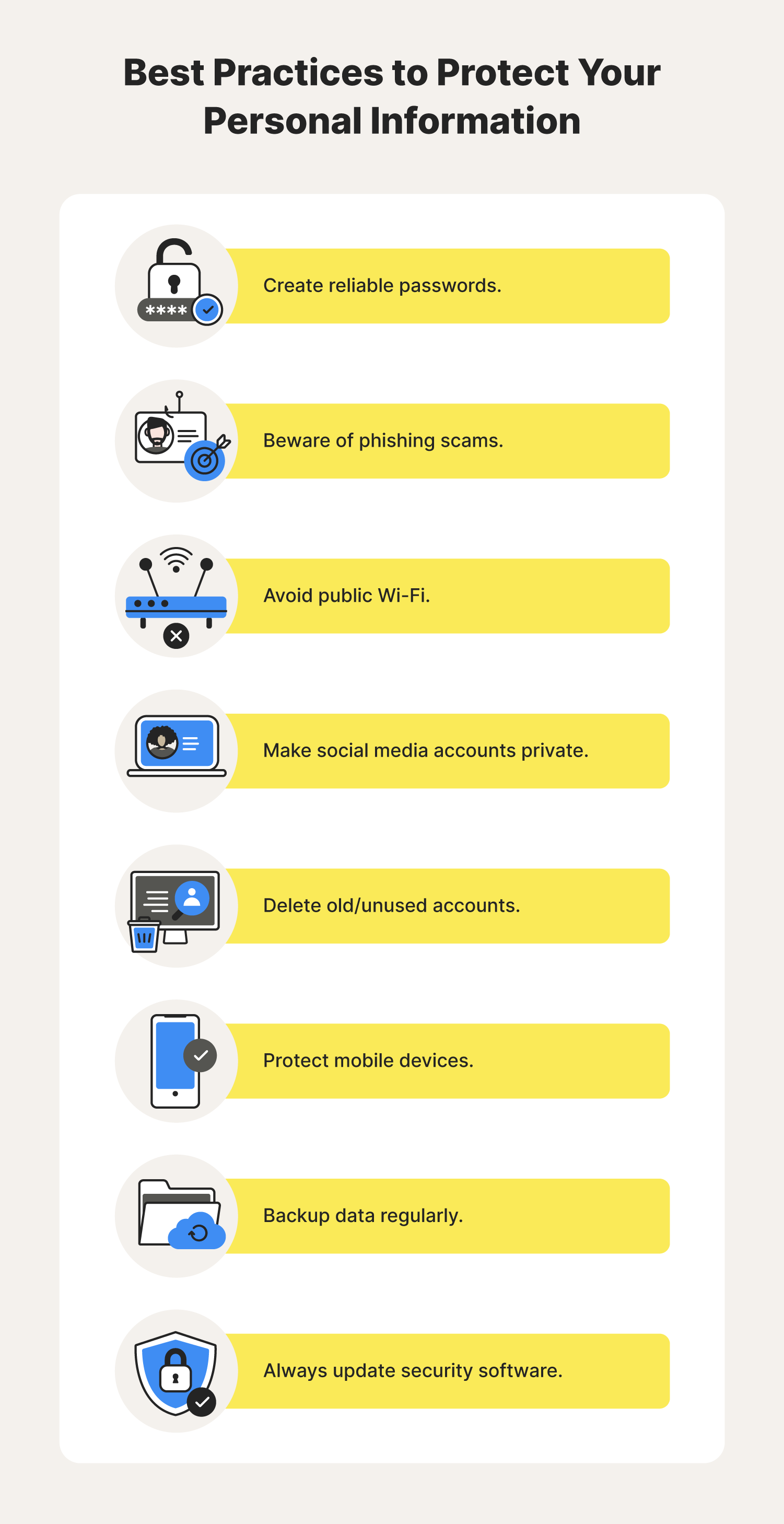
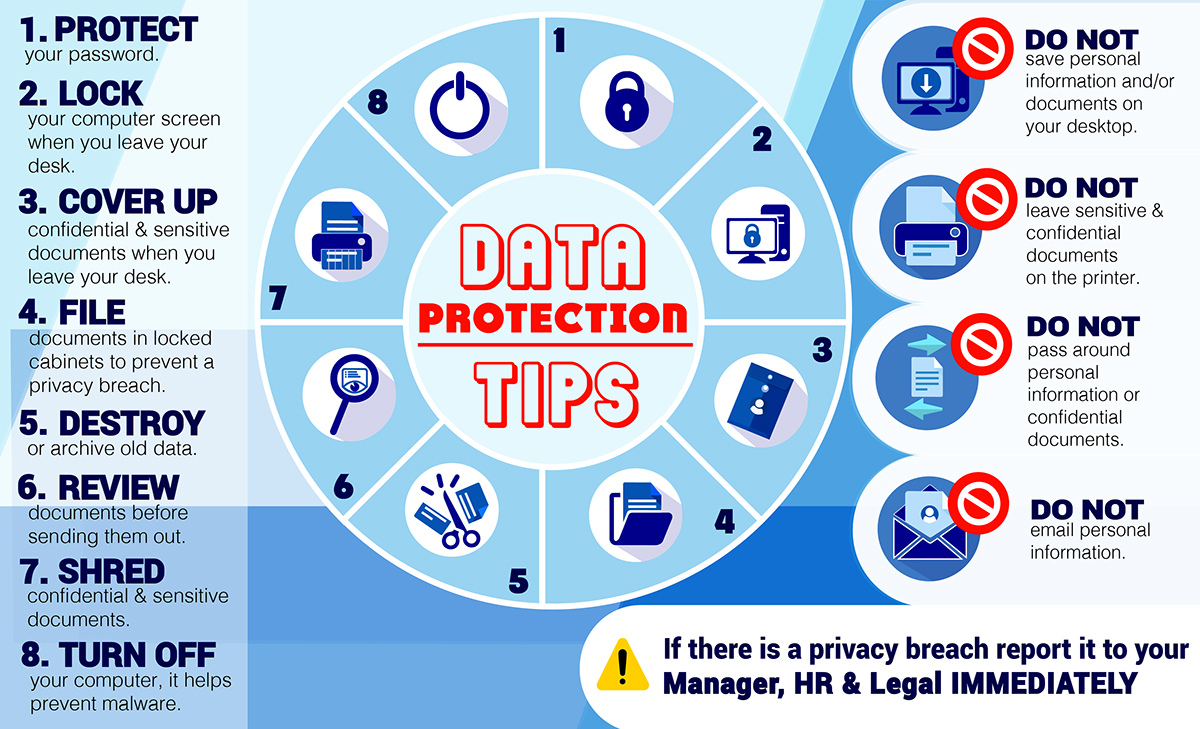
Best Practices for Data Protection
By implementing these data protection techniques, you can ensure the safety and security of your personal data. Additionally, follow these best practices:
- Use strong, unique passwords for all online accounts
- Enable 2FA whenever possible
- Keep your operating system and software up-to-date
- Be cautious when clicking on links or downloading attachments from unknown sources
- Use a reputable VPN service to secure online activity
- Monitor your accounts and credit reports regularly for suspicious activity
Conclusion
Data protection is a critical aspect of maintaining online security and privacy. By implementing the above data protection techniques and best practices, you can safeguard your sensitive information and protect yourself from data breaches and identity theft. Remember, data protection is an ongoing process that requires regular monitoring and maintenance to ensure the security of your personal data.