Effective Ways to Protect Against Malware and Trojan
Malware is one of the biggest threats to the security of your computer, tablet, phone, and other devices. It can cause significant damage, steal sensitive information, and disrupt normal operations. In this article, we will discuss some effective ways to protect yourself against malware and Trojan threats.
Understand Malware and Trojan Threats
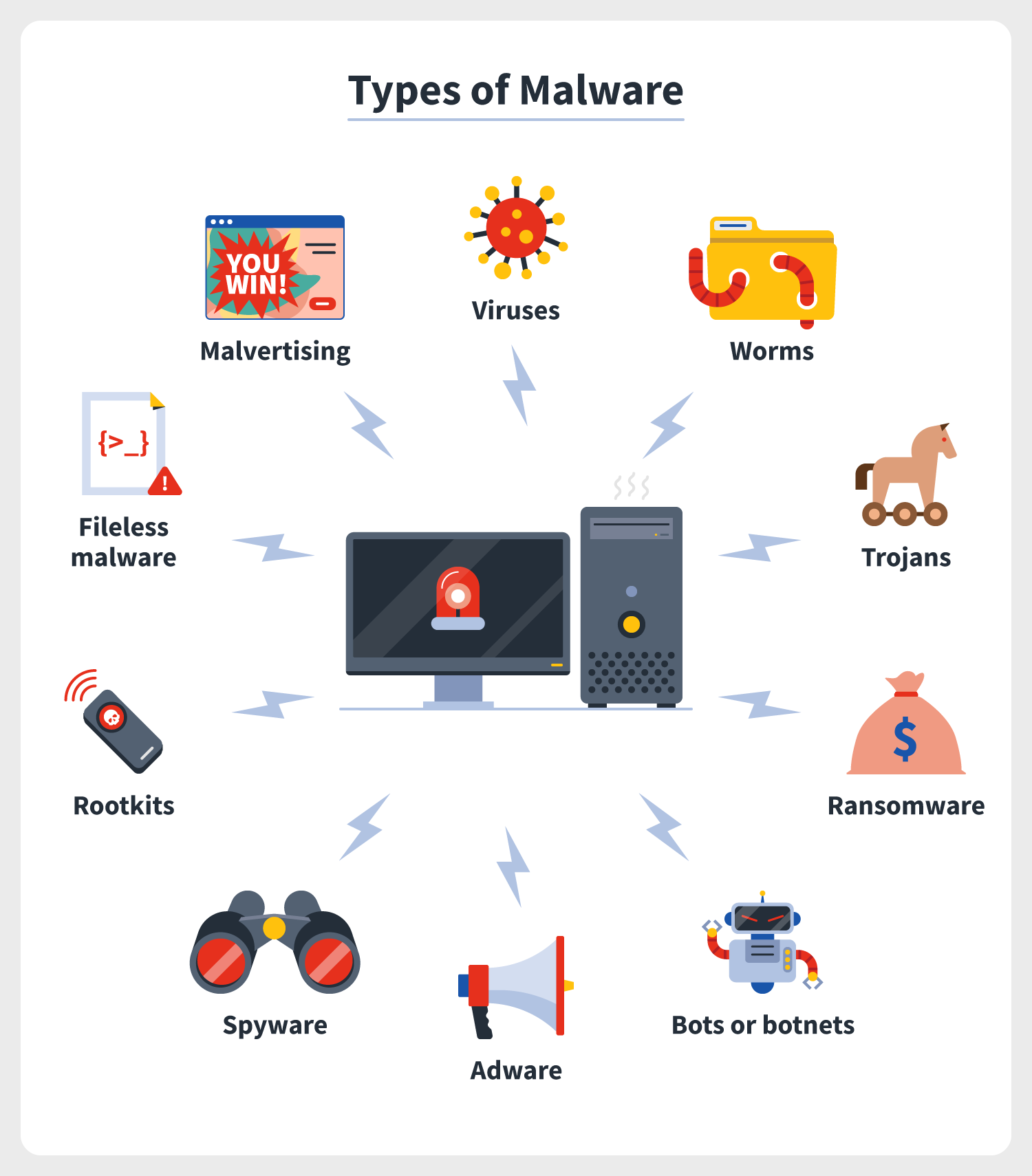
A malware is a type of malicious software that is designed to harm or exploit computer systems. It can be used to steal sensitive information, install unwanted programs, or disrupt system operations. Trojan horses, or Trojan for short, are a type of malware that disguises itself as legitimate software to fool users into downloading it onto their devices.
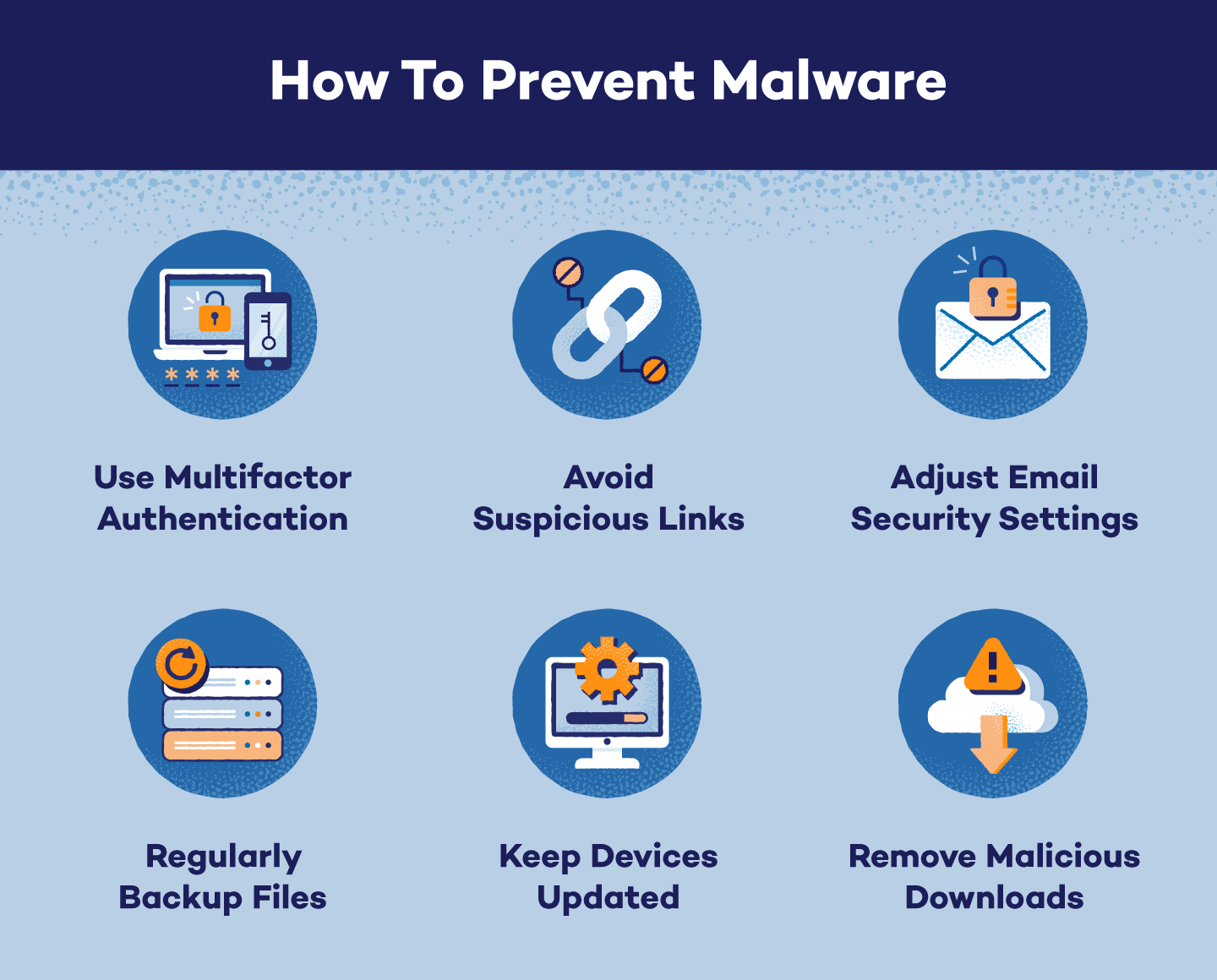
Prevention is the Best Defense
Preventing malware and Trojan infections is always better than trying to remove them after they have happened. Here are some effective ways to prevent malware and Trojan infections:
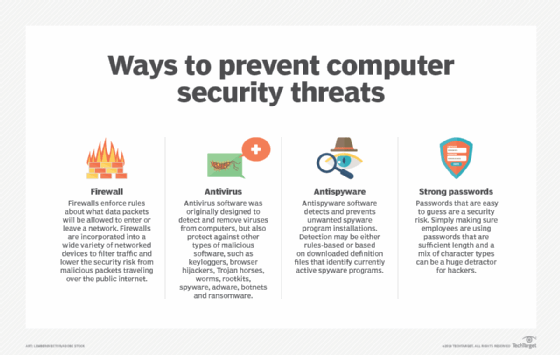
- Use a reliable antivirus program: Install an antivirus program that is regularly updated to protect against the latest malware threats.
- Keep your operating system and software up to date: Regularly update your operating system and software to patch security vulnerabilities and fix bugs.
- Be cautious with email attachments and links: Avoid opening suspicious email attachments and links, as they may contain malware.
- Use strong passwords: Use strong passwords for your accounts and change them regularly to prevent unauthorized access.
- Use a firewall: Enable the firewall on your device to block unauthorized access to your system.
Real-Time Protection
Real-time protection is a feature that can provide protection against malware and Trojan threats in real-time. It scans all incoming network data for malware and blocks any threats it comes across. This type of protection is similar to antivirus protection, but it works in real-time to prevent malware infections.
Detection and Removal

Even with prevention measures in place, malware and Trojan infections can still occur. Here are some steps to detect and remove malware and Trojan infections:
- Run a full system scan: Run a full system scan using your antivirus program to detect any malware or Trojan infections.
- Identify and quarantining infected files: Identify and quarantine infected files to prevent them from causing further damage.
- Remove infected programs: Remove any infected programs or apps from your device.
- Reinstall your operating system: In severe cases, you may need to reinstall your operating system to completely remove malware and Trojan infections.
Conclusion
Malware and Trojan threats are a significant concern for computer users, as they can cause significant damage and disrupt normal operations. By following the effective ways to protect against malware and Trojan infections discussed in this article, you can significantly reduce the risk of malware and Trojan infections on your device. Remember to always use a reliable antivirus program, keep your operating system and software up to date, be cautious with email attachments and links, use strong passwords, use a firewall, and detect and remove malware and Trojan infections promptly.
Additional Resources
For more information on malware and Trojan threats, visit the following resources:
- IBM Security: Leveraging educational content on emerging security and identity technologies.
- Microsoft Security Response Center Blog: staying up to date with the latest security threats and best practices.
- Fortra's data loss prevention software: discover, monitor, and block sensitive data across endpoints, cloud, and SaaS apps.
- Avast Free Antivirus software: detects, blocks, and removes all types of malware: viruses, adware, spyware, Trojans, and more.
Take Action Today
Don't wait until it's too late. Take action today to protect yourself against malware and Trojan threats. Install a reliable antivirus program, keep your operating system and software up to date, and be cautious with email attachments and links. Remember, prevention is the best defense against malware and Trojan infections.