Ransomware Protection For Cloud: The Ultimate Guide to Ensuring Data Security
The Soaring Threat of Ransomware in Cloud Environments
Ransomware has become one of the most significant threats to cloud computing in recent years, with attack costs projected to reach a staggering $74 billion in 2026. The cloud is no longer a safe haven from these malicious attacks, and companies must take proactive measures to protect their sensitive data. In this article, we will delve into the world of ransomware protection for cloud and explore the best practices for safeguarding your cloud workloads.What is Ransomware Protection for Cloud?
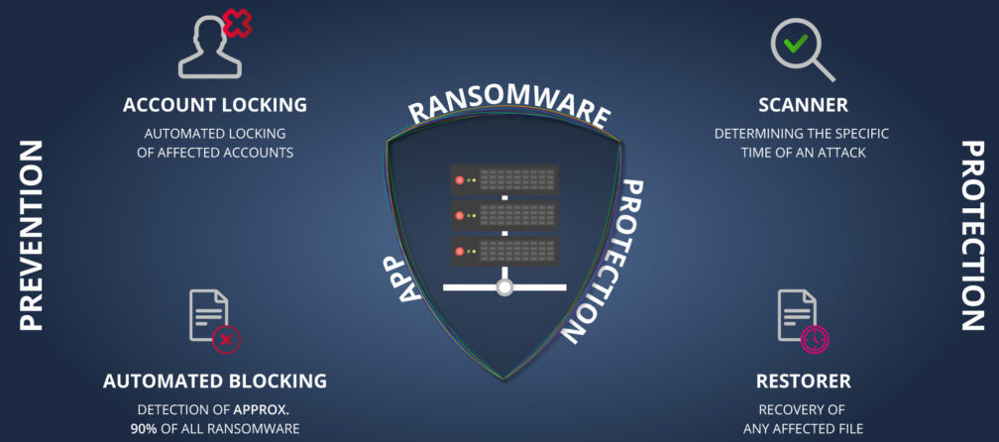
Ransomware protection for cloud refers to the set of measures and technologies that prevent, detect, and respond to ransomware attacks in cloud environments. It involves implementing security controls, monitoring systems, and recovery strategies to ensure the integrity and availability of cloud data. Ransomware is a type of malware that targets data in cloud environments by exploiting features and APIs to encrypt, exfiltrate, or destroy data.Key Features of Ransomware Protection for Cloud
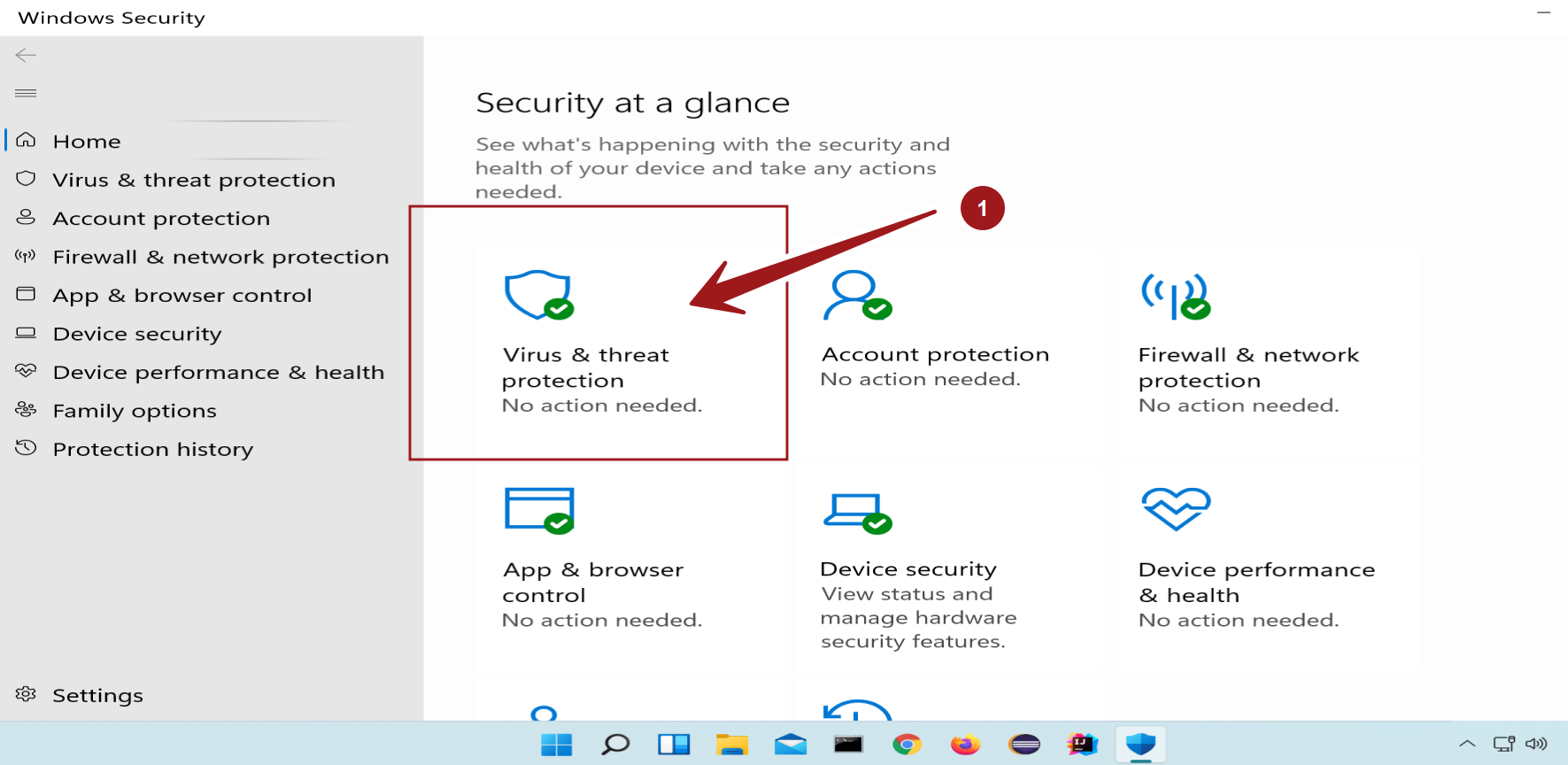
A comprehensive ransomware protection for cloud solution should include the following key features: * Cloud Native Security Capabilities: Invest in native security capabilities that provide real-time threat detection, vulnerability assessment, and intrusion detection. * Backup and Recovery: Implement a robust backup and recovery strategy that ensures rapid data recovery in the event of a ransomware attack. * Behavioral Monitoring: Leverage behavioral monitoring to detect and block ransomware by analyzing user behavior and system activity. * Cloud-Based Encryption: Utilize cloud-based encryption to protect data at rest and in transit, ensuring the confidentiality and integrity of sensitive information. * Regular Security Updates: Implement regular security updates and patch management to ensure that vulnerabilities are addressed and weaknesses are eliminated.Best Practices for Ransomware Protection in Cloud