Protecting Yourself from Position Impersonators: A Comprehensive Guide
Understanding the Threat of Position Impersonators
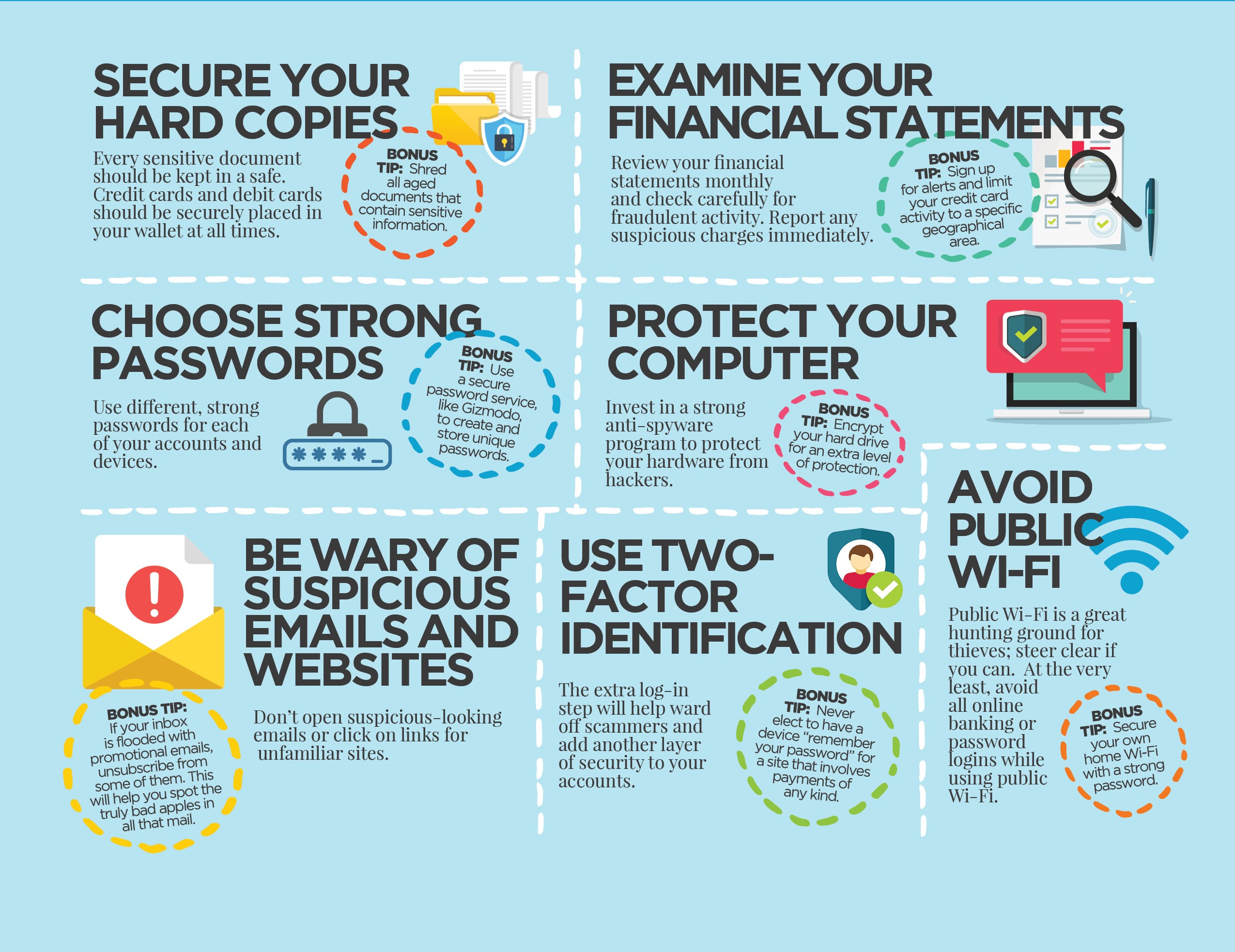
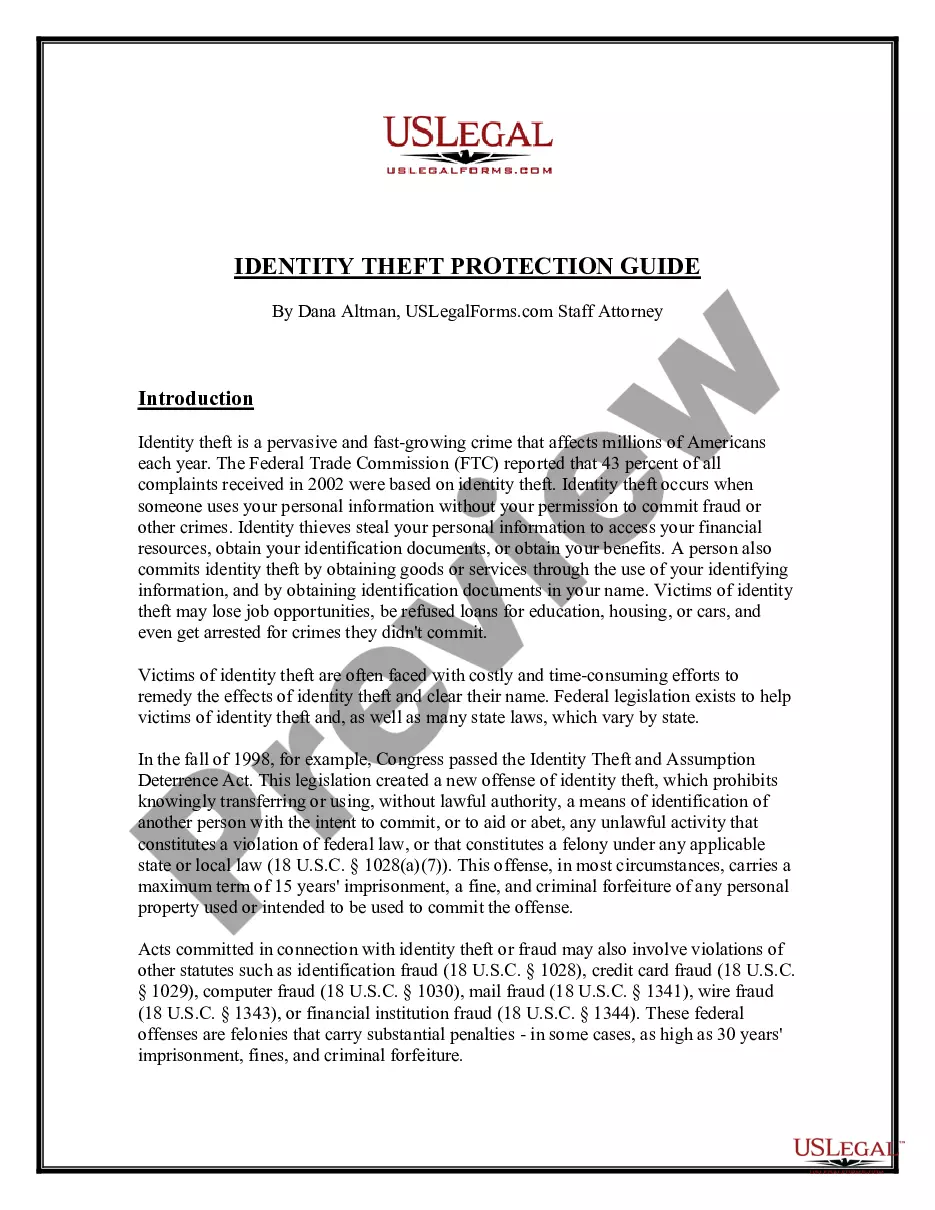
In today's digital age, impersonation attacks are on the rise, targeting executives, finance teams, and legal professionals. These scams can have devastating consequences, including financial loss, reputational damage, and emotional distress. It's essential to understand the tactics employed by position impersonators and how to protect yourself and your organization.Common Types of Position Impersonation
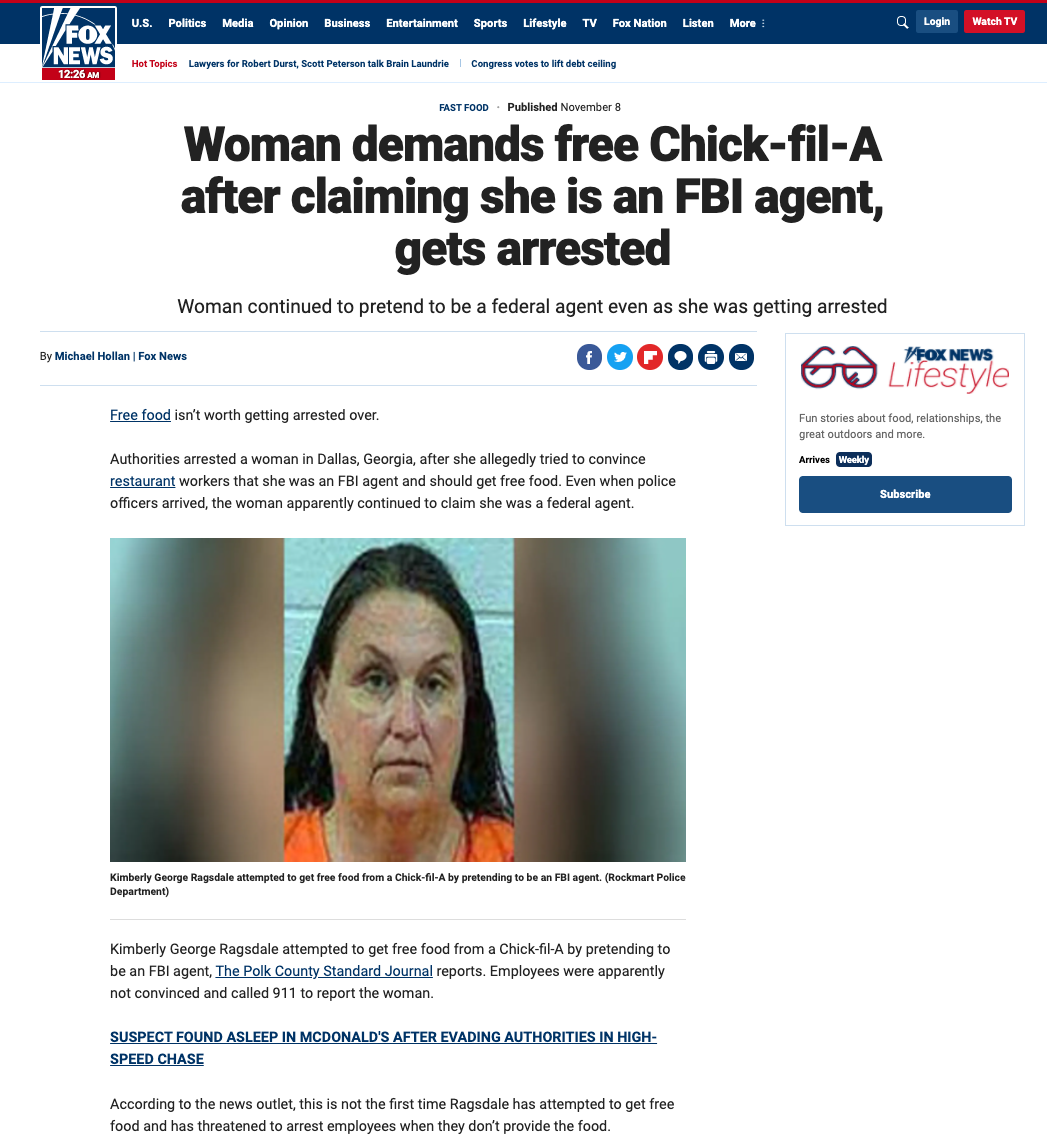
Position impersonation involves assuming another person's identity to deceive others. Scammers can impersonate employees or managers of small businesses to trick legitimate employees into providing sensitive information, transferring money, and/or granting access to a business's systems or network. Other common types of position impersonation include: * Phone scams (vishing) * Email scams (phishing) * Social media impersonation * Identity theftHow Position Impersonators Operate