Protecting Your Online Identity from Data Breaches
Data breaches have become a pressing concern in today's digital age. With the increasing reliance on technology, our sensitive information is more vulnerable than ever to unauthorized access. However, taking steps to protect yourself can help mitigate the risk of identity theft and keep your online presence secure. In this article, we will explore the importance of protecting your online identity from data breaches and provide practical advice on how to safeguard your digital life.
Understanding Data Breaches
A data breach occurs when sensitive information is stolen or accessed without authorization. This can happen due to hacking, phishing, or even insider threats. Data breaches can result in the exposure of personal details such as names, email addresses, passwords, and financial information. Such exposed data can be used to commit identity theft and other forms of financial fraud.
Symptoms of a Data Breach
- Receiving unsolicited emails or messages asking for sensitive information
- Unexplained charges on your credit or debit card
- Receiving a notification from your bank or credit card company about unusual activity
- Not receiving expected mail or tax refunds
Protecting Your Online Identity
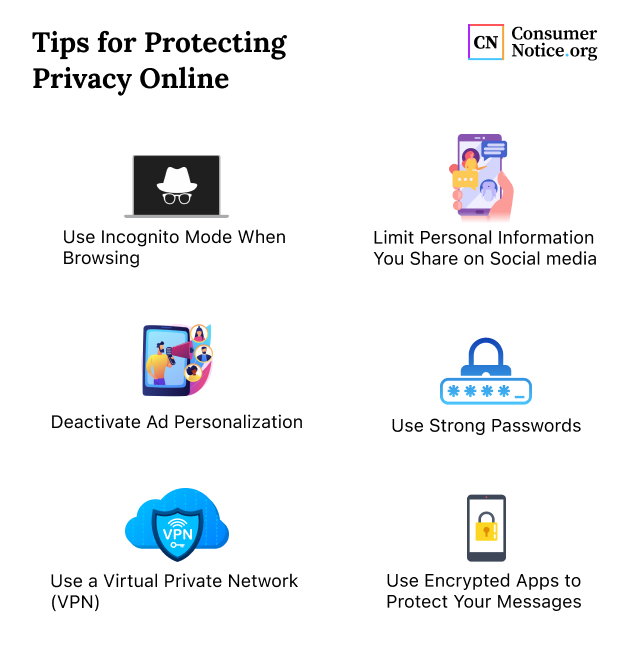
Protecting your online identity from data breaches requires a combination of awareness, vigilance, and proactive measures. Here are some essential steps to safeguard your personal information:
1. Use Strong Passwords and 2FA
Use unique and complex passwords for all online accounts, and consider using a reputable password manager. Enable two-factor authentication (2FA) whenever possible to add an extra layer of security to your accounts. This will make it more challenging for hackers to access your information, even if they obtain your password.
2. Be Cautious with Emails and Links
Phishing attacks can lead to data breaches. Be wary of suspicious emails and avoid clicking on links or downloading attachments from unknown sources. If an email seems too good to be true or asks for sensitive information, it's best to delete it.
3. Regularly Update Your Software
Keep your operating system, browser, and other software up-to-date to ensure you have the latest security patches and updates. This will help prevent exploitation of vulnerabilities that hackers can exploit to gain access to your device.
4. Monitor Your Accounts and Credit Reports
Regularly review your bank and credit card statements for any unusual activity, and check your credit reports for any new accounts or inquiries.

5. Consider Identity Theft Protection Services
Identity theft protection services can offer an added layer of security, alerting you to potential breaches and providing monitoring and assistance in case of a breach. Some popular services include Aura, LifeLock, and Identity Guard.
6. Educate Yourself and Others
Stay informed about the latest cyber threats and online risks. Educate family and friends on the importance of online security and encourage them to take proactive steps to protect themselves as well.
What to Do If You're a Victim of a Data Breach
If you suspect your information has been compromised in a data breach, take the following steps:
1. Change Passwords and 2FA
Immediately change your passwords and 2FA settings for all accounts affected by the breach. This will help prevent hackers from accessing your accounts with your compromised credentials.
2. Monitor Your Accounts and Credit Reports
Keep a close eye on your bank and credit card statements, and check your credit reports for any suspicious activity.
3. Contact theTrust Organization
Reach out to the organization or company experiencing the breach to report the incident and understand what steps they are taking to address the breach.
4. Consider Reporting Identity Theft
File a report with the Federal Trade Commission (FTC) and the credit reporting agencies to report the identity theft and seek assistance in resolving the issue.