How to Protect Your Data from Hacking Attempts: A Comprehensive Guide
In today's digital age, protecting your data from hacking attempts is more crucial than ever. With cyber threats on the rise, everyone from individuals to organizations needs to take proactive measures to safeguard their sensitive information. In this article, we will delve into the best practices for preventing hacking attempts and provide you with actionable tips to protect your data.
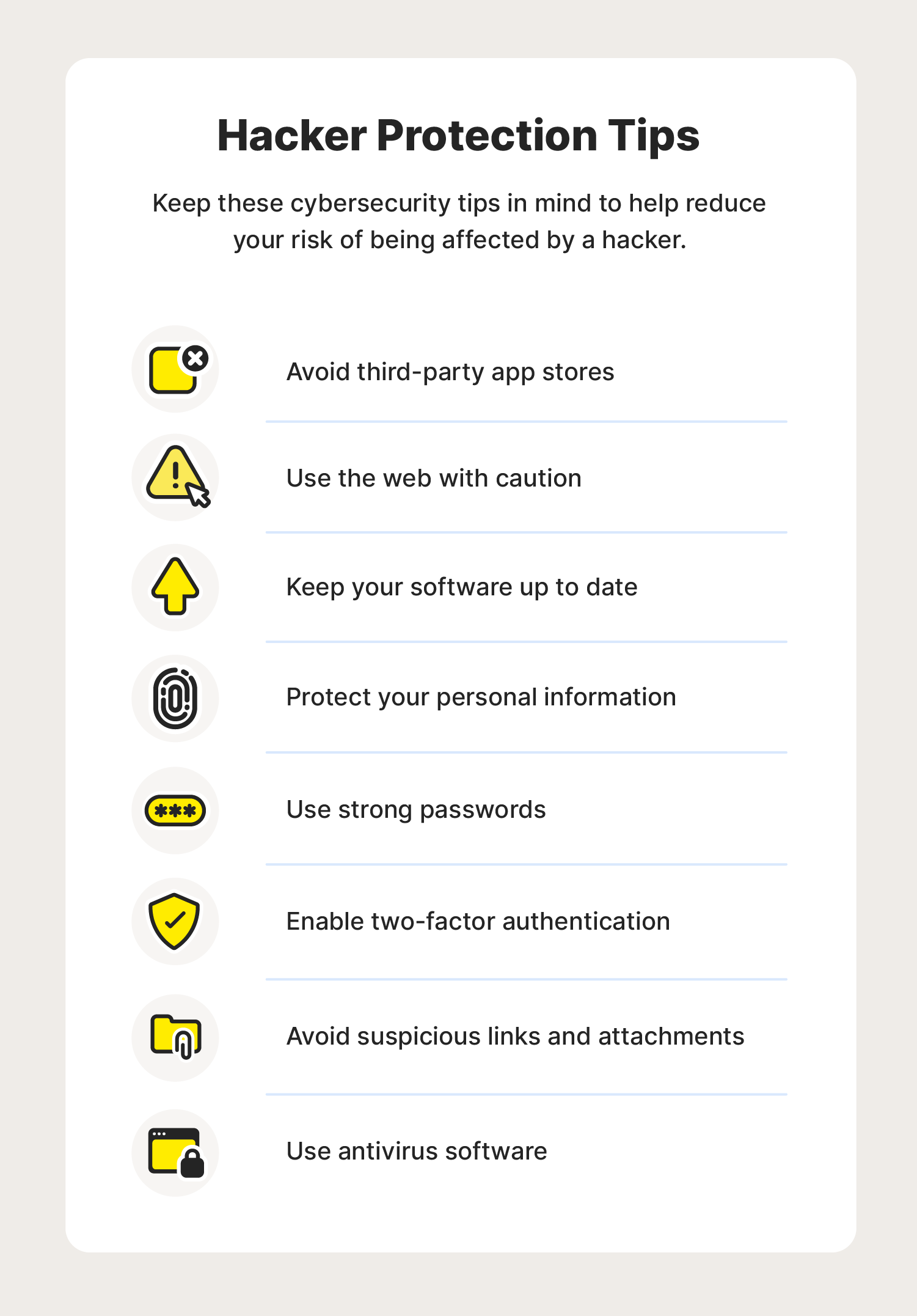
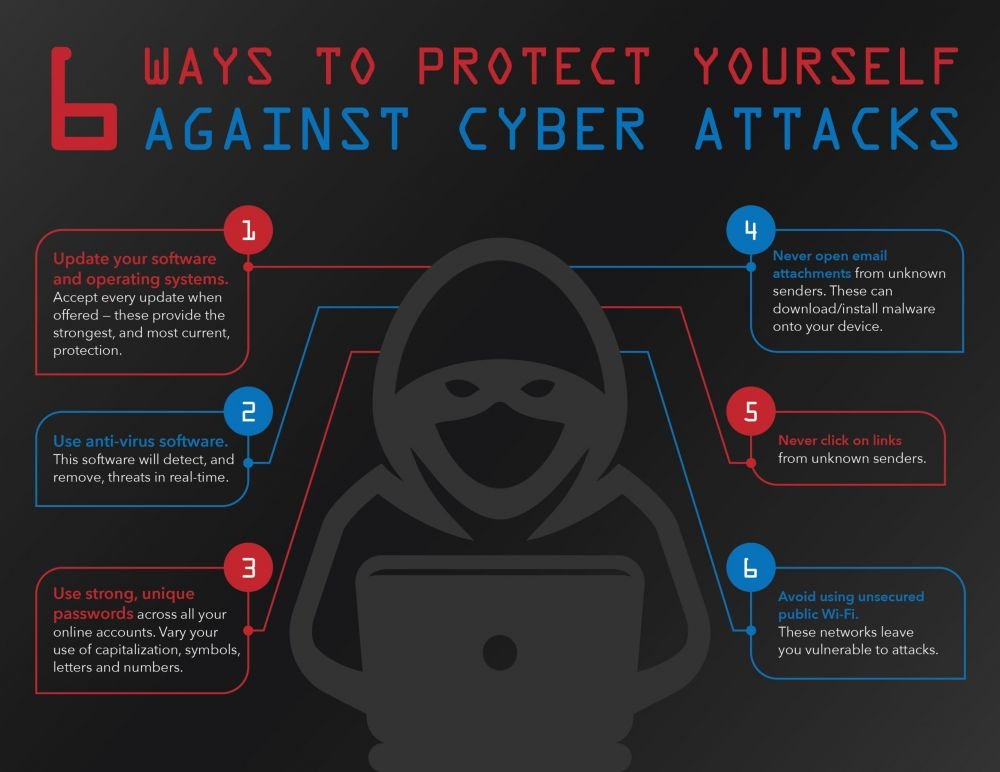
Strong passwords are the first line of defense
Weak passwords are the easiest entry point for hackers to gain access to your data. To protect yourself, use strong and unique passwords for all your online accounts. A strong password should be a combination of letters, numbers, and special characters, making it difficult for hackers to crack. Consider using a password manager to generate and store complex passwords.
- Create a strong password with a combination of upper and lower case letters, numbers, and special characters
- Use a password manager to generate and store complex passwords
- Change your passwords regularly (every 60-90 days) to minimize the risk of hacking attempts
Enable two-factor authentication (2FA)
2FA adds an extra layer of security to your online accounts by requiring a verification code sent to your phone or email in addition to your password. This makes it much harder for hackers to gain access to your data. Turn on 2FA for all your online accounts, including email, banking, and social media.
- Turn on 2FA for all your online accounts, including email, banking, and social media
- Use an authenticator app like Google Authenticator or Authy to generate 2FA codes
- Store your 2FA secrets in a secure location, such as a password manager
Monitor your accounts and devices regularly
Regular monitoring of your accounts and devices can help you detect and prevent hacking attempts. Keep an eye out for suspicious activity, such as login attempts from unfamiliar locations or unauthorized transactions. Use antivirus software and a firewall to protect your devices from malware and unauthorized access.
- Regularly check your bank statements and credit reports for suspicious activity
- Use antivirus software and a firewall to protect your devices from malware and unauthorized access
- Keep your operating system and software up-to-date with the latest security patches
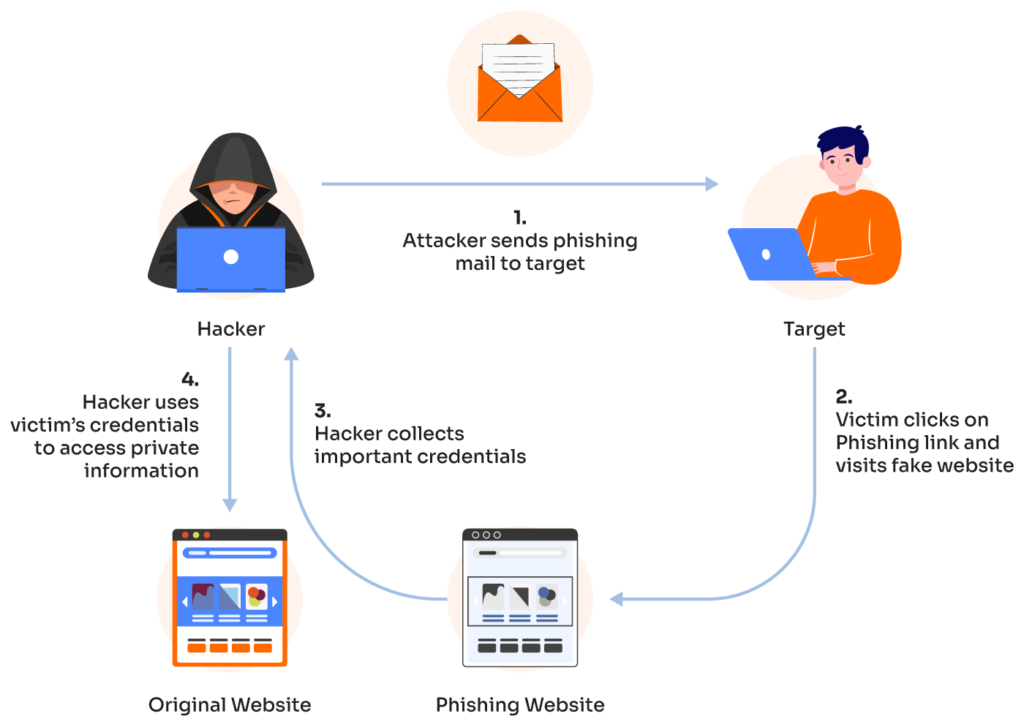
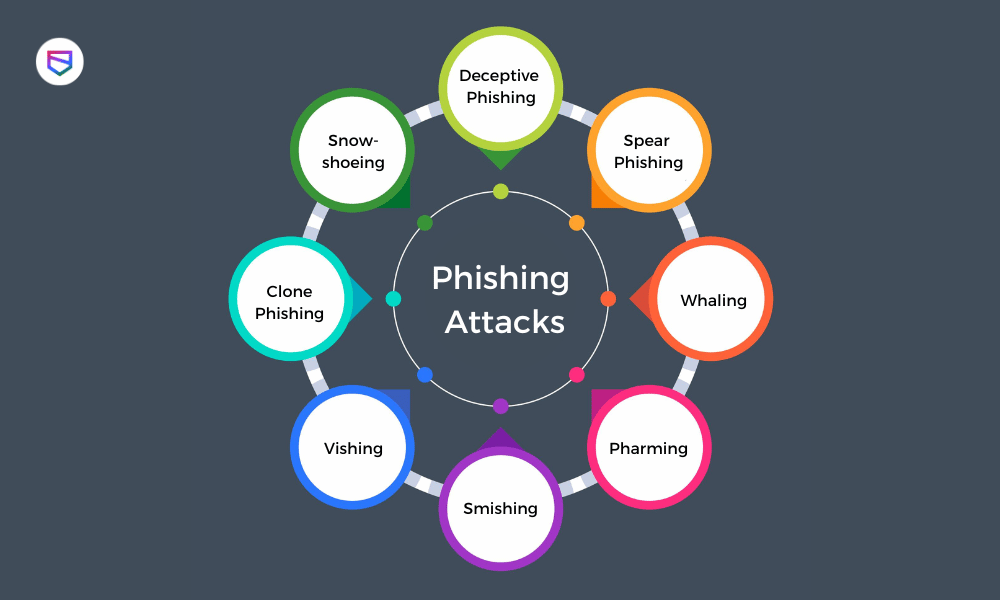
Be cautious of phishing and social engineering attacks
Phishing and social engineering attacks are common hacking attempts that involve deception and trickery. Be wary of suspicious emails, messages, or phone calls that ask for sensitive information or try to create a sense of urgency. Never click on suspicious links or provide sensitive information via email or phone.
- Be cautious of suspicious emails, messages, or phone calls that ask for sensitive information
- Verify the authenticity of emails and messages before clicking on links or providing sensitive information
- Use a spam filter and a secure email client to reduce the risk of phishing attacks
Use encryption to protect sensitive data
Encryption is a powerful tool for protecting sensitive data from hacking attempts. Use encryption to protect sensitive information, such as financial data or personal health information. Consider using a reputable VPN service to encrypt your internet traffic and protect your data in transit.
- Use encryption to protect sensitive information, such as financial data or personal health information
- Consider using a reputable VPN service to encrypt your internet traffic and protect your data in transit
- Use a secure file transfer protocol (SFTP) to transfer sensitive files
Stay informed and up-to-date
Staying informed and up-to-date with the latest cybersecurity threats and best practices is crucial for protecting your data from hacking attempts. Follow reputable cybersecurity sources, attend webinars and conferences, and participate in online forums to stay informed.
- Follow reputable cybersecurity sources, such as BleepingComputer and Verizon Media
- Attend webinars and conferences to stay informed about the latest cybersecurity threats and best practices
- Participate in online forums and discussion groups to stay informed and connect with other cybersecurity professionals